In networks where the variety of uses can be counted in the thousands, how can the IT team distinguish between legitimate network flows, anomalies due to configuration or performance errors, and behaviors to due to attacks and threats? In a time of zero-day attacks, BYOD policies, and open networks, it has become even more crucial for IT professionals to anticipate such events and to be ready and able to respond within minutes.
With its ability to trace all network flows, Skylight™ is a deep source of insights for isolating anomalies in network and application behavior, and mitigating risks before they impact end-users or IT security.
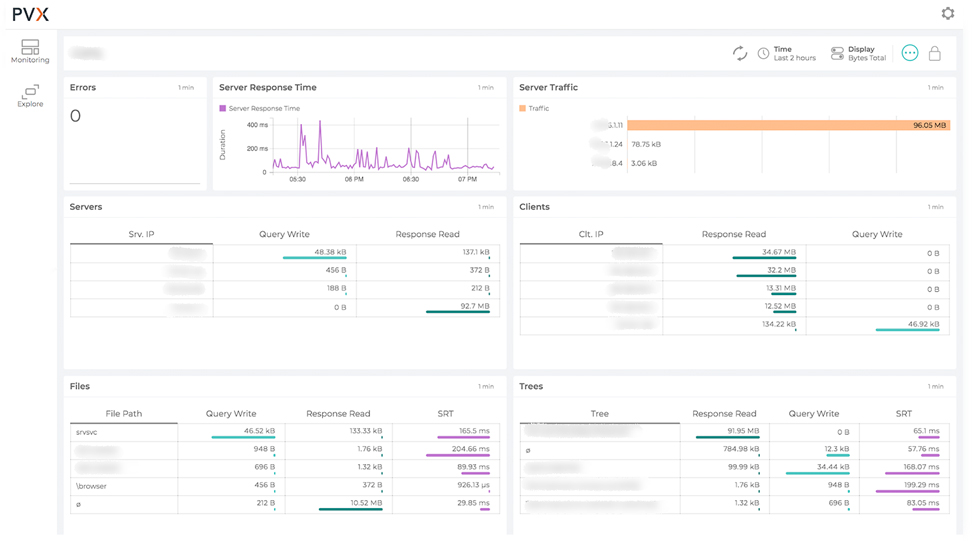
Skylight sensors tracks all network flows and application transactions, enabling IT teams to quickly and easily isolate behaviors such as:
- Misuse of network resources related to recreational or unforeseen application behaviors
- Misconfigurations of different types, including traffic flowing outside of normal time windows (e.g., backups), traffic flowing over the WAN (when it is supposed to remain inside a LAN / data center), and system configurations generating abnormal traffic (e.g., system or antivirus updates)
- Viral threats such as ransomware, cryptolockers, and worms that generate recognizable network traffic even though they cannot yet be recognized by system-level protections
Skylight sensors parse and analyze all network flow data (e.g., NetFlow, sFlow, jFlow, IPFix, etc.)—in addition to complete wire data inspection at the packet level—in order to detect abnormal behaviors and alert the IT team to phenomena such as:
- Traffic to non-existing network segments
- One-way traffic
- Traffic to abnormal network services / ports
- Changes in the number of destinations / transactions generated by clients
- Users logging into resources they have never accessed before

 Improved delivery, better visibility: How Accedian and VMware are working together to help CSPs navigate the 5G world
Improved delivery, better visibility: How Accedian and VMware are working together to help CSPs navigate the 5G world
 Adding a new dimension of visibility to the Cisco Full-Stack Observability portfolio with Accedian Skylight
Adding a new dimension of visibility to the Cisco Full-Stack Observability portfolio with Accedian Skylight